Network Firewalls, Network Access Control
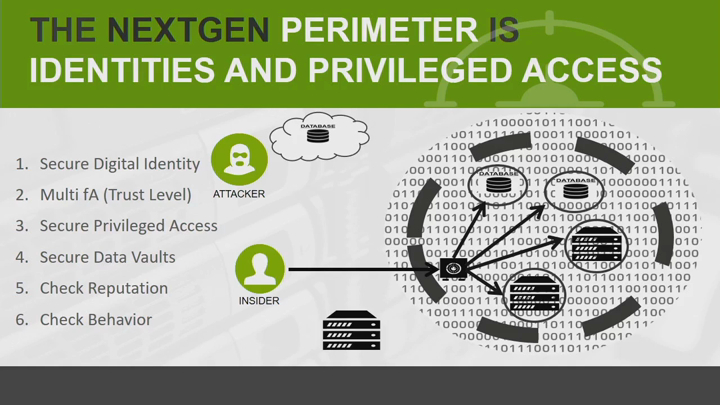
The Evolution of Perimeter Security: Where Are The New Boundaries?

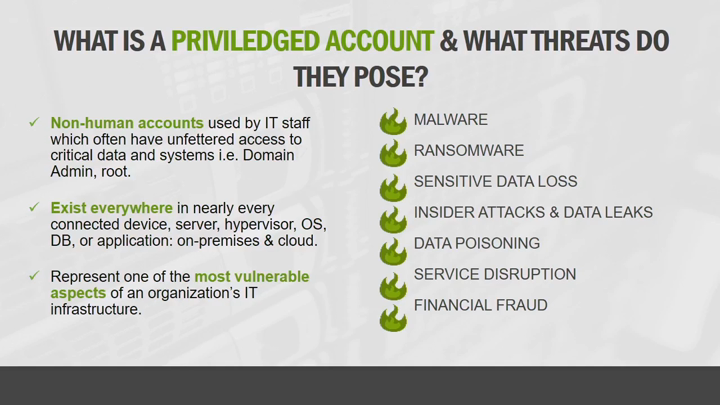
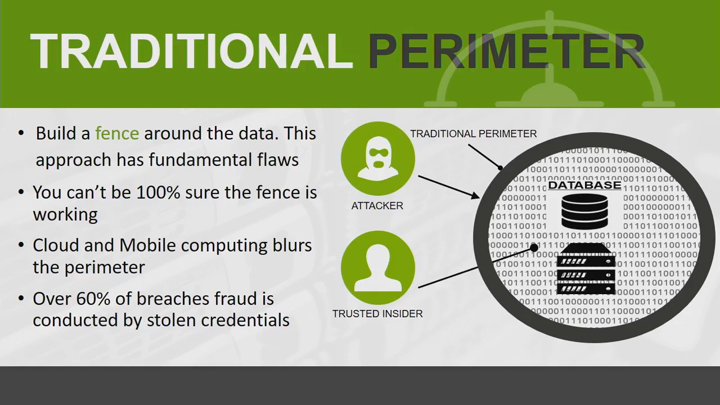
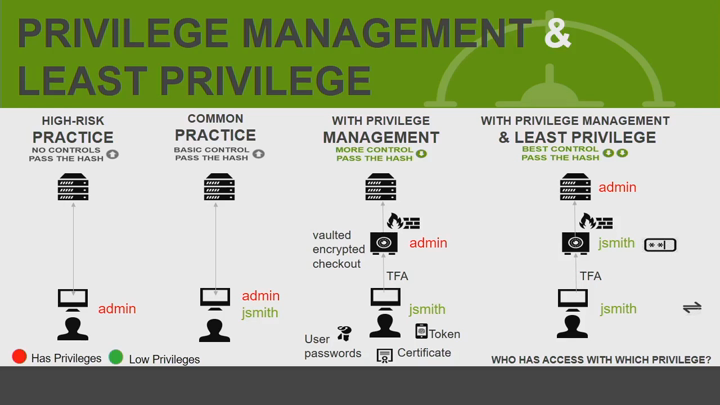
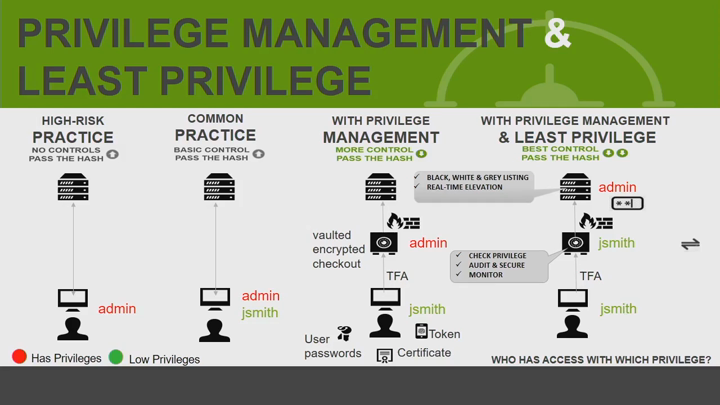
Why do we continue to see so many cyber breaches? If we look at why most cyber breaches of the past year occurred, we see that it comes down to three major factors - the human factor, identities and credentials, and vulnerabilities. Living in a digital social society, we share more information, ultimately exposing ourselves to social-engineering and targeted spear-phishing attacks waged to compromise our systems for financial fraud or steal our identities to access trusted corporate information. The perimeter has moved and we need to move with it. Learn about how identity and access management are evolving and becoming the new security perimeter.
See Also: Enhanced Security Resilience for Federal Government
Additional Summit Insight:
Hear from more industry influencers, earn CPE credits, and network with leaders of technology at our global events. Learn more at our Fraud & Breach Prevention Events site.